

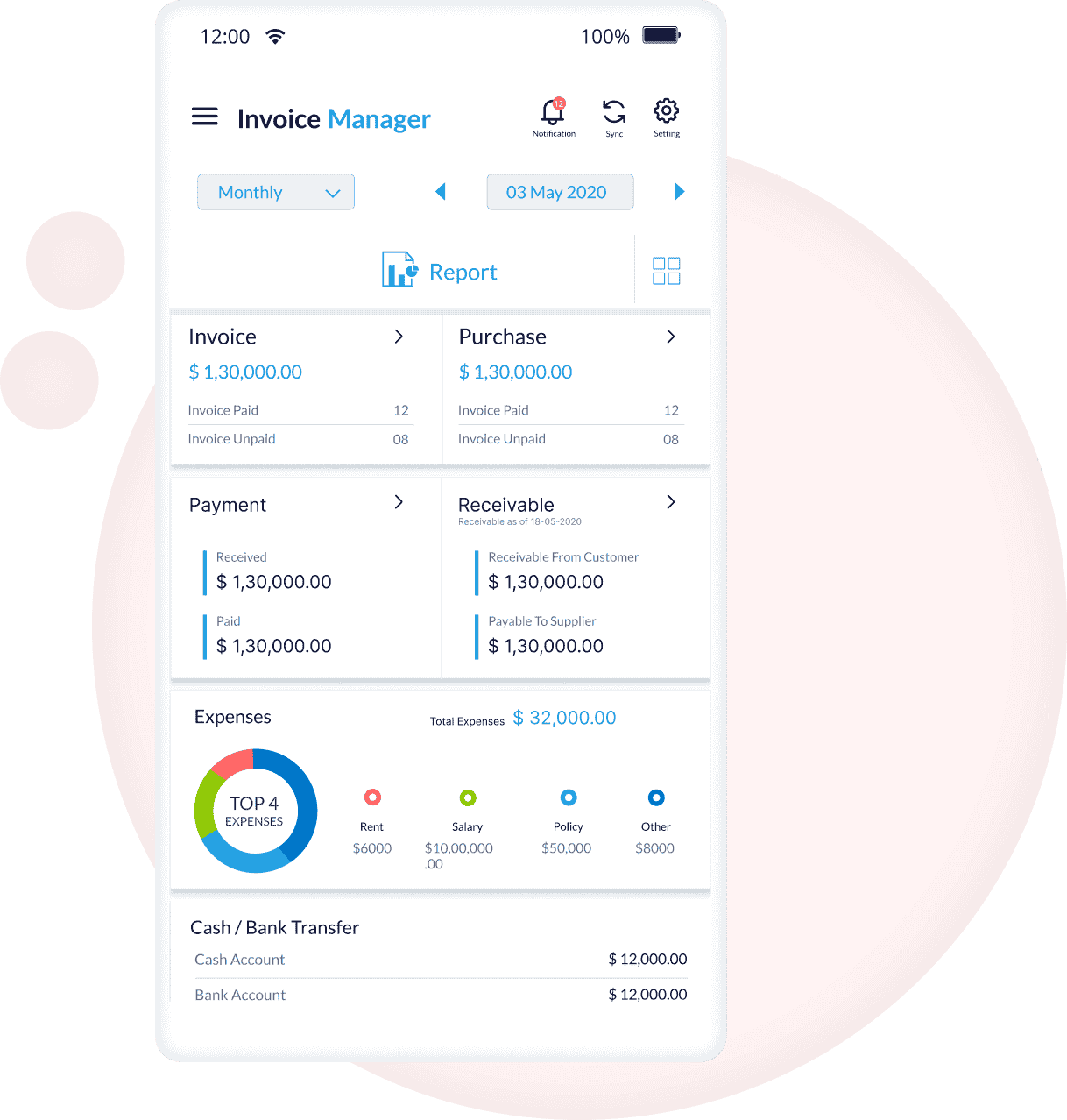
Best invoicing, billing and accounting software for small businesses, freelancers and service providers. Manage entire business with Simple Invoice Manager. Create professional invoices, manage billing, track payments and maintain accounts effortlessly.
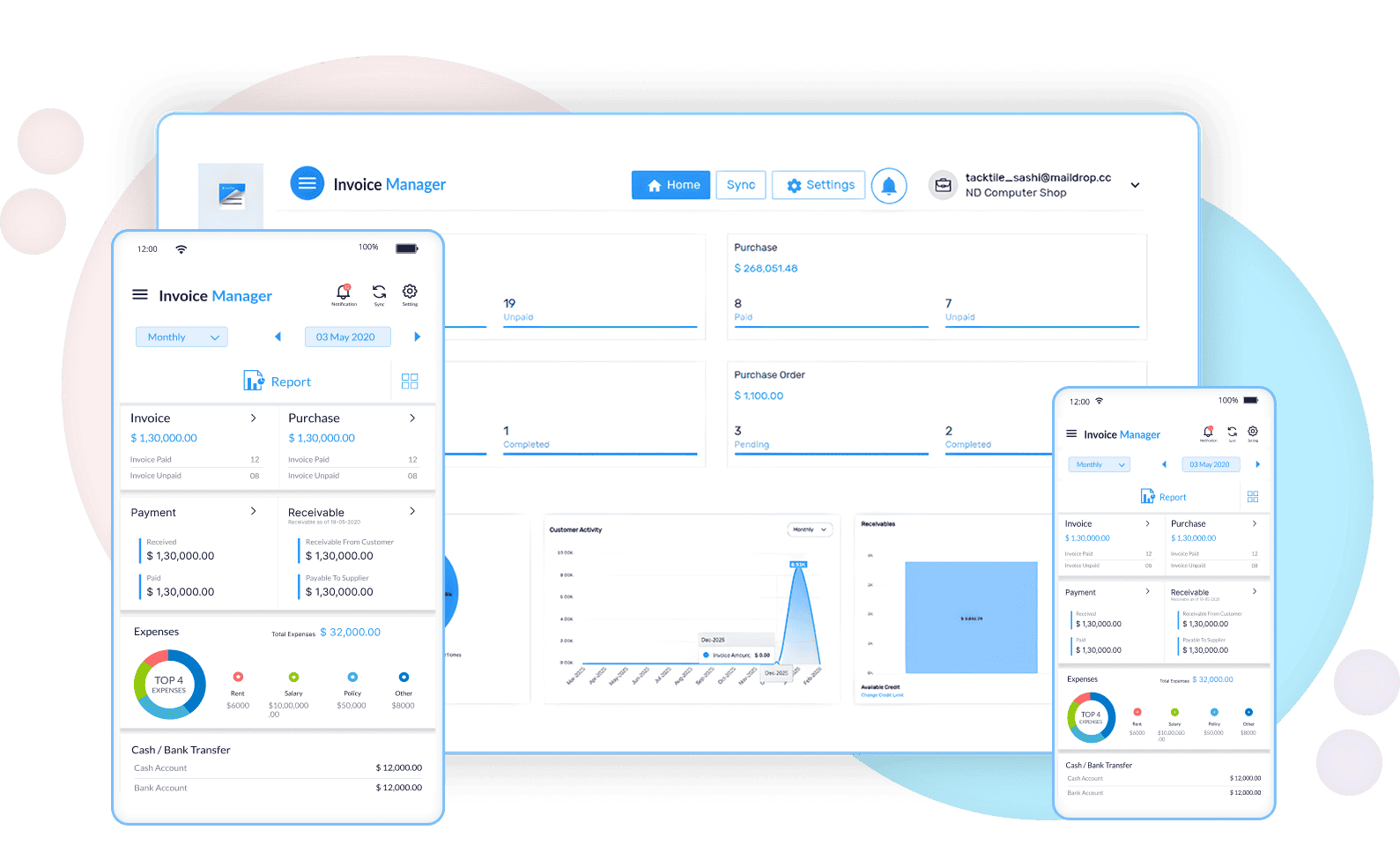
Simple Invoice Manager is a complete invoicing, billing & accounting software designed specifically for small businesses, freelancers, and startups. Create professional invoices in seconds, track payments, manage GST compliance, and maintain detailed financial records all in one place.
Whether you're a retailer, service provider, or accountant, Simple Invoice Manager provides all the tools you need to streamline your invoicing and billing process efficiently.
Whether you bill hourly, per project, or sell physical products — generate clean, professional invoices effortlessly.
Reduce delays and improve cash flow with structured billing management. cyberhack pb
Get clarity on your business performance without hiring expensive accounting software. When Mara logged off that night, the city hummed, unaware
Automated quarterly reporting.
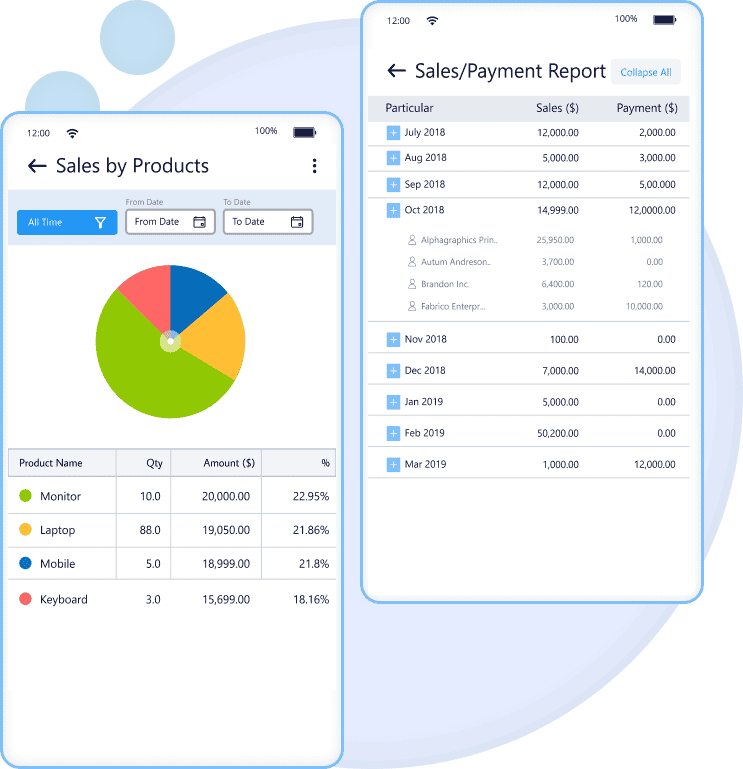
Track top performing services.
Real-time outgoing management.
Instant tax-ready breakdowns.
Simple Invoice Manager also includes additional tools that integrate seamlessly with your invoicing workflow
Create customizable invoices with automatic numbering and PDF export.
Automate subscription and repeat invoices effortlessly.
Track paid, unpaid and overdue invoices in real time.
Profit & loss, sales reports, tax summaries and dashboards.
Track stock levels and receive low-stock alerts instantly.
Turn your device into a powerful retail POS system.
Assign roles and manage sub-users securely.
Access your data anywhere with encrypted cloud storage.
Designed to scale with your business — from solo entrepreneur to growing team.
Send professional invoices and track payments easily without the overhead.
Manage billing, expenses, inventory, and reports in one centralized system.
Automate recurring billing and monitor revenue growth across your client base.
Seamlessly integrate POS billing with real-time inventory tracking.
Simple tools. Professional results.
Your financial data is your most sensitive asset. We protect it using bank-grade 256-bit encryption and redundant cloud infrastructure.
When Mara logged off that night, the city hummed, unaware. On her desk lay a single printed sheet—her report—edges curling from the heat of the radiator. She circled a final note in ink: “Close the obvious doors. Teach people to see the hidden ones.” Then she packed her bag and walked into the dark, already thinking three moves ahead.
The first layer was almost polite. An employee’s reused password—birthday plus pet name—opened a back door. An automated backup system, misconfigured and trusting, whispered its credentials like a lover at midnight. Mara slipped through and found herself in a room of mirrors: replicas of production, sandboxed logs, pretend data. They’d expected theatrics. They hadn’t expected curiosity.
The board heard the word “confidence” and bristled. They wanted absolutes. Cybersecurity rarely offers them. So she framed it differently: risk, not blame. She mapped a path forward—patches ordered by impact, monitoring tuned to the new normal, contracts rewritten to force vendor hygiene. She proposed something they hadn’t budgeted for: an internal red-team program run monthly, not just once a year, and a promised culture shift where developers and security were fellow architects, not adversaries.
They called it a test—a simulation tucked behind corporate firewalls and glossy mission statements. To the board, Cyberhack PB was a drill: a controlled breach meant to expose weaknesses and measure responses. To Mara, it was an invitation.
She froze, mind racing through containment playbooks. This was the moment drills were supposed to prevent: the point where mock danger met the real thing. Mara took control of the timeline. She injected a breadcrumb—an elegant, noisy trap designed to slow and expose. The traffic balked and reshaped. Whoever was on the other end adjusted, but the delay bought Mara time to trace the connection to an IP range masked by rented servers.
She followed the breadcrumbs outward, peeling layers of obfuscation. The trail wasn’t sophisticated—mostly commodity tools and recycled scripts—but it was hungry, persistent. A small syndicate outsourcing its labor to freelancers overseas, a money trail routed through wallets that vanished like smoke. In the margins she found something worse: credentials sold on a low-tier forum, the same accounts she’d accessed legally for the test. The lines between mock breach and market had blurred.
Weeks later, during a tabletop exercise, a junior engineer raised a hand. “What if the attacker used supply chain attacks?” she asked. Mara’s answer was the same she gave in every room: keep moving, keep probing, and treat every trust relationship as negotiable. “Assume compromise,” she said. “Design to limit blast radius.”
Cyberhack PB would be stamped in the company’s log as a successful exercise—metrics met, recommendations offered. But for those who witnessed the breach grow from simulation to threat and back again, it became a lesson in humility. Security, like any craft, was as much an art as a science: an endless practice of anticipating the unpredictable and answering not with panic, but with precision.
When Mara logged off that night, the city hummed, unaware. On her desk lay a single printed sheet—her report—edges curling from the heat of the radiator. She circled a final note in ink: “Close the obvious doors. Teach people to see the hidden ones.” Then she packed her bag and walked into the dark, already thinking three moves ahead.
The first layer was almost polite. An employee’s reused password—birthday plus pet name—opened a back door. An automated backup system, misconfigured and trusting, whispered its credentials like a lover at midnight. Mara slipped through and found herself in a room of mirrors: replicas of production, sandboxed logs, pretend data. They’d expected theatrics. They hadn’t expected curiosity.
The board heard the word “confidence” and bristled. They wanted absolutes. Cybersecurity rarely offers them. So she framed it differently: risk, not blame. She mapped a path forward—patches ordered by impact, monitoring tuned to the new normal, contracts rewritten to force vendor hygiene. She proposed something they hadn’t budgeted for: an internal red-team program run monthly, not just once a year, and a promised culture shift where developers and security were fellow architects, not adversaries.
They called it a test—a simulation tucked behind corporate firewalls and glossy mission statements. To the board, Cyberhack PB was a drill: a controlled breach meant to expose weaknesses and measure responses. To Mara, it was an invitation.
She froze, mind racing through containment playbooks. This was the moment drills were supposed to prevent: the point where mock danger met the real thing. Mara took control of the timeline. She injected a breadcrumb—an elegant, noisy trap designed to slow and expose. The traffic balked and reshaped. Whoever was on the other end adjusted, but the delay bought Mara time to trace the connection to an IP range masked by rented servers.
She followed the breadcrumbs outward, peeling layers of obfuscation. The trail wasn’t sophisticated—mostly commodity tools and recycled scripts—but it was hungry, persistent. A small syndicate outsourcing its labor to freelancers overseas, a money trail routed through wallets that vanished like smoke. In the margins she found something worse: credentials sold on a low-tier forum, the same accounts she’d accessed legally for the test. The lines between mock breach and market had blurred.
Weeks later, during a tabletop exercise, a junior engineer raised a hand. “What if the attacker used supply chain attacks?” she asked. Mara’s answer was the same she gave in every room: keep moving, keep probing, and treat every trust relationship as negotiable. “Assume compromise,” she said. “Design to limit blast radius.”
Cyberhack PB would be stamped in the company’s log as a successful exercise—metrics met, recommendations offered. But for those who witnessed the breach grow from simulation to threat and back again, it became a lesson in humility. Security, like any craft, was as much an art as a science: an endless practice of anticipating the unpredictable and answering not with panic, but with precision.